
The MITRE ATT&CK is a documented collection of information about patterns of malicious behavior used by advanced persistent threat (APT) groups during real-world cyberattacks. ATT&CK, or Adversarial Tactics, Techniques, and Common Knowledge, describes the observed tactics (the technical objectives they’re trying to achieve), techniques (the ways they do it), and procedures (the way they do it), often called TTPs.
MITRE ATT&CK is not a threat model in the traditional sense (it doesn’t compare with PASTA, 1 STRIDE2 or OCTAVE3), but it is commonly used as a basis for organizations to develop their own customized threat models. It is an encyclopedic guide to TTPs adversaries use, provides suggestions for detection and common mitigations to deal with specific techniques, and profiles APT groups’ known practices, characteristics, and specific attack attributes. ATT&CK provides a comprehensive listing of software used in attacks (both malware and commercially available software as well as open-source software).
Information collected in ATT&CK comes from publicly available data and reports as well as from the community of threat researchers and security teams who experience and analyze attacks on a daily basis.

Depending on their target, attackers operate differently. To compromise enterprise systems, they would use different tactics than they would to attack mobile devices or industrial control systems. To address these different environments, MITRE provides three separate “matrices”. Together these three matrices form what MITRE collectively refers to as the ATT&CK framework.
Among the Enterprise matrix’s components are platforms such as Windows, macOS, Linux, and others, as well as something called “PRE,” which indicates actions taken prior to an attack. The Mobile matrix addresses both Android and iOS, and the ICS matrix addresses industrial control systems. While the three matrices share some tactics (Initial Access and Persistence, for example), the specific tactics for each tactic can vary depending on the environment.
This article primarily focuses on the Enterprise matrix. Its sheer size and density can be overwhelming at first glance (see Figure 1).
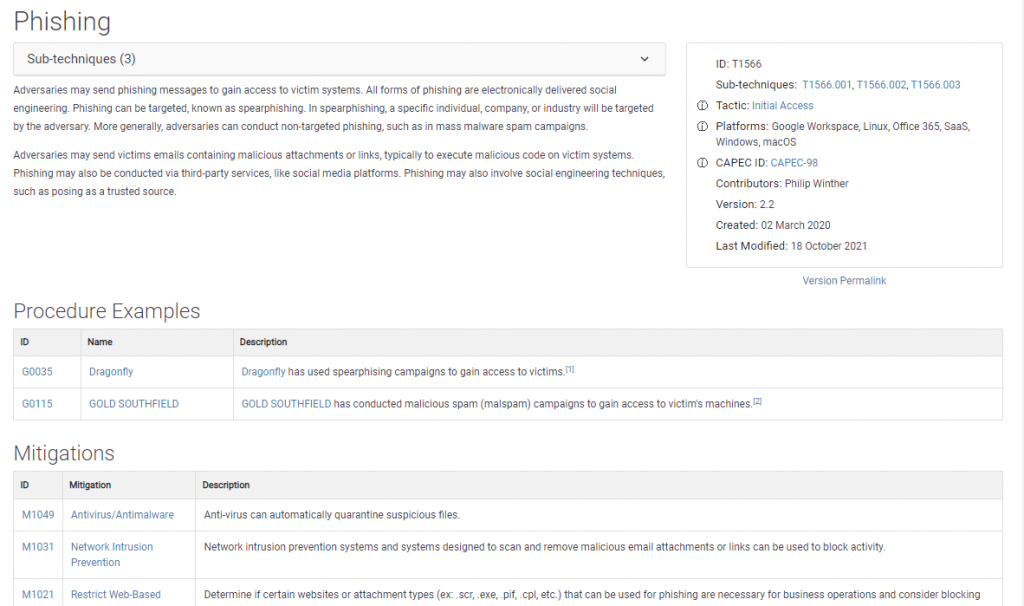
Figure 1
As a spreadsheet, the term matrix can also be misleading if you expect row widths to match column widths. The full matrix becomes a lot less intimidating when you realize the 14 independent columns are structured more like individual organization charts (see Figure 2). Below each tactic are associated techniques and sub-techniques.

Figure 2
ATT&CK is a free tool widely used by both public and private sector organizations of all sizes and industries. Users include security defenders, penetration testers, red teams, and cyberthreat intelligence teams. In addition to internal teams interested in building secure systems, applications, and services. Organizations can use this information to determine if they’re gathering the right data to detect attacks and to evaluate how well their current defenses are working.
To help organizations better understand how adversaries approach, prepare for, and execute attacks. ATT&CK intentionally adopts an attacker’s perspective, unlike other models written from a defender’s perspective. It is also a great resource and teaching tool for individuals interested in entering the field of cybersecurity or threat intelligence. As well as those who simply wish to understand more about attacker behavior.
Though the information captured in ATT&CK reflects known APT behaviors. It would be a mistake to assume that those behaviors are exclusive to APTs. In Ray Pompon’s words, “What APTs are doing today, script kids will be doing tomorrow”. This means organizations that are not the target of APTs and have never experienced APT-like attacks can benefit from ATT&CK. ATT&CK outlines the TTPs that happen every day in organizations of all sizes and significance. To experience the same kinds of attacks or to use the ATT&CK tool to improve your defenses. You don’t need to be a target of an APT.
Prior to MITRE releasing ATT&CK, there was no single, holistic repository of adversary TTPs. Elite and national security operators were largely focused on forensic, historical attributes of adversary intrusions such as code that proved the adversary had already been inside the network; the nature of these signatures and indicators of compromise meant that organizations were constrained by needing to protect their intelligence sources and methods, and that made it harder for them to share information broadly.
The “kill-chain” methodology, first developed by Lockheed Martin in 2011. Which maps out the specific phases that an adversary follows, step-by-step, as it approaches an asset to attack, from reconnaissance to weapons deployment to command and control to actions on the objective. By understanding the kill-chain (a term originally coined in the military), defenders can better position their security controls to mount an effective defense.
While Lockheed Martin pioneered the kill-chain methodology. MITRE analyzed adversary TTPs in depth and developed a framework for defenders to focus on threats that matter most. Since then, the framework has gained significant momentum in the public and private sectors as a globally vetted, all-source repository of adversary threat behaviors. Public and private sectors have responded well to ATT&CK. ATT&CK transforms organizations from taking an ad hoc approach to security operations to adopting a data-driven, threat-informed approach — and it has caught on globally
ATT&CK can be divided into three “flavors” or matrices. The most popular one and the one we will discuss here is:
Enterprise ATT&CK
PRE-ATT&CK – includes pre-compromise tactics and techniques that attackers use before they exploit the target network,
Mobile ATT&CK – a model of adversarial tactics and techniques for gaining access to mobile devices.
MITRE Corporation, a not-for-profit that supports several government agencies, began developing ATT&CK in 2013. Originally released in May 2015. The Adversarial Tactics, Techniques, and Common Knowledge framework has been updated on a quarterly basis since then.
MITRE ATT&CK Lead Blake Strom says the framework was developed to better document adversary behaviors within FMX, an internal research project. Apart from behaviors, the group sought a way to classify how attackers interacted with systems across all groups in real-time.
Both blue and red teams can benefit from ATT&CK. The adversarial emulation plans from ATT&CK are appropriate for red teams to test their networks and defenses by modeling off of adversary behavior. Tracking ATT&CK campaigns provides insight into attacks, deciphers patterns, and measures the effectiveness of existing defenses.
Blue teams can utilize the AT&CK framework to better understand what adversaries are doing, prioritize threats, and ensure the right mitigations are in place.
ATT&CK benefits enterprises by enhancing post-compromise detection of malicious actors seeking to undermine their core assets. By using ATT&CK, organizations gain insight into the actions an attacker might take. Things such as how the attacker entered the system, how they are moving around, and what areas they are targeting become apparent.
The knowledgebase answers key questions about how hackers target specific companies as well as contributing to overall organizational security posture. ATT&CK enables companies to identify holes and vulnerabilities, based on the overall risk.
There are too many specific techniques to list here – over 290 in particular – but these are some of the top ATT&CK tactics that businesses can employ to strengthen their cybersecurity posture.
The most common form of malware attack in the matrix, process injection involves inserting active code into a system for malicious purposes. After that, the code will do several things, such as disable systems for ransomware purposes or automatically steal data. For new ATT&CK users, simulating process injection is a great place to start.
Hackers love PowerShell attacks because it’s the interface that system administrators use to manage and configure their operating systems. It is a scripting language and command-line shell installed by default on Windows. So any company relying on Windows should strongly consider using MITRE ATT&CK exercises with PowerShell.
Cybercriminals have access to extremely powerful tools – such as Mimikatz – designed to either guess passwords or bypass authentication altogether. By phishing or social engineering, hackers gather credentials by asking or forcing users to provide authentication information.
Hackers often alter malware’s appearance to make it appear legitimate and trustworthy. Code signatures, names, and locations of malware files, and the names of tasks and services are just a few examples. MITRE ATT&CK exercises can help you find out how hackers might disguise themselves in your system and how to weed them out more effectively.
An adversary’s first objective after gaining access to a system is to find credentials to access other resources and systems in the environment. Credential dumping is an effective way to obtain account login and password information, making it one of the top tactics to use in the ATT&CK matrix to prevent unauthorized access.
We should understand what MITRE ATT&CK means by tactics, techniques, and procedures before diving into the matrix, since these terms can have different meanings in other contexts.
Tactics: A description of the immediate technical objectives (the “what”) attackers are trying to accomplish, such as gaining access, maintaining persistence, and establishing command and control. To be successful in an attack, attackers typically employ multiple tactics.
Techniques: Describes the “how”-that is, the methods attackers use to accomplish a tactic. In each matrix, each tactic has multiple techniques. Several Enterprise techniques further subdivided into sub-techniques. Attackers use phishing techniques to gain initial access (a tactic). Phishing has three associated sub-techniques: Spear phishing Attachment, Spear phishing Link, and Spear phishing via Service.
Procedures: Describes the specific implementations of techniques and sub-techniques used by APTs, or it can refer to malware or other tools used by attackers.
ATT&CK’s most recent version includes 14 tactics listed in a logical order. Indicating the possible phases of an attack.1 They are:
The foundation of the work hinges on CTI provided by the ATT&CK framework and the CTI your team develops. Either from its own forensic work or from external sources available either from vendors or open-source intelligence. ATT&CK is a framework outlining the probable tactics that adversaries use to deploy against your enterprise. To use threat intelligence and MITRE ATT&CK, you must first understand the adversary by studying its behaviors. After that, you focus on which adversaries target your sectors and the TTPs they use.
From there, you can build threat intelligence to prepare your defenses against adversary TTPs. After you understand how to use CTI, you begin the process of integrating analytics. Within your enterprise, you have event logs, scripts, and cybersecurity capabilities that track adversary behavior. You can collect the information about adversary TTPs into your security information and event management (SIEM) tool to then run analysis about adversary tactics and assess results about the adversary’s behavior. This process requires that you write detections, revise to filter out false positives, and ensure search detections. It takes work, but, step by step, you build your analysis and detection capabilities. You can integrate blue and red teams to run combined operations in a purple team with ATT&CK as a base.
This process follows these steps:
This process requires that you assess how your defenses perform, identify your gaps in coverage, determine how to close the gaps, and then modify your defenses accordingly. Blue and red teams work closely together in the process and work across the security operations center to detect and prevent attacks from succeeding.
You can operationalize ATT&CK by using a breach-and-attack simulation platform for continuous, automated security control validation safely, in production environments, and at scale across your enterprise. Security controls are the people, processes, and technologies that defend your network against intrusions, and these controls often fail for two reasons: user error and misconfiguration. Security controls should have prevented 82 percent of enterprise breaches after decades of cybersecurity investment, but did not.
The only way to know if security controls are working at any point in time is to test them. To solve this problem, in the past, security teams used red teams (penetration teams) to test their defenses, but they were sporadic and unable to scale across the enterprise. A penetration test conducted six months ago against less than one-tenth of your enterprise’s total security controls tells you nothing about the effectiveness of your cybersecurity platform today. With ATT&CK as a foundation, you can direct your security teams to focus their security controls on the most probable methods of adversary attack. Continual, automated testing ensures security controls focus on what matters most and ensures that they are effective. Automation generates real performance data from across your enterprise that your security teams can use to improve your overall effectiveness
The ATT&CK framework can be useful for any organization that wants to move toward a threat-informed defense strategy. You can benefit from threat intelligence and MITRE ATT&CK in the following ways:
» Identify key hostile actors, using a globally vetted framework.
» Gain insight into adversaries’ operational behavior to analyze how that impacts your cyberdefenses.
» Deepen your approach by comparing your results to other analysts.
» Strengthen your defense teams by focusing on countering known hostile actors
Getting your hands on the ATT&CK matrix and seeing the depth of data it provides is the best way to learn about it. Let’s start by zooming into a partial view of the matrix shown in Figure 1. This Figure (3) shows Reconnaissance, Resource Development, and Initial Access are the three first tactics in the Enterprise matrix, accompanied by Techniques under each tactic. Those entries with a gray bar on the right contain sub-techniques, whose numbers appear in parentheses following the technique name.
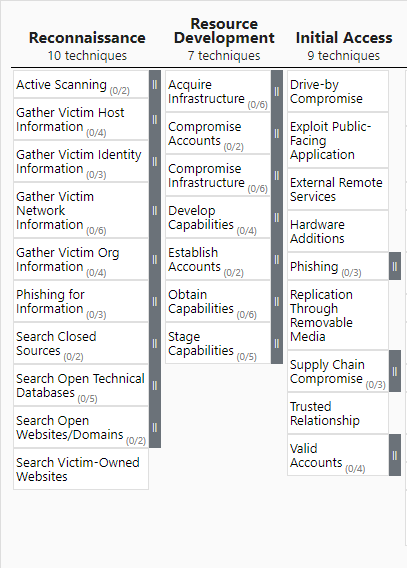
Figure 3
A tactic’s detail page includes a general description, as well as all the methods and sub methods that belong to it. The tactic ID number, date created, and date last modified are listed in the metadata to the right of the description. Figure 4 shows three of the nine techniques on the Initial Access detail page. Under Techniques, each entry has a unique ID number and distinct name (both clickable).

Figure 4
Each technique has a similar detail page. On the matrix, click on the Phishing entry under Initial Access (As shown in figure 5) to see more details about this technique. An overview of the technique appears on the technique detail page, along with significantly more metadata than appears on the tactics detail page. The metadata includes the three sub-technique numbers, the tactic this technique belongs to, the platforms it applies to, and the data sources you might use to detect this type of activity. A list of Procedure Examples follows the description, which explains how specific APTs have utilized this technique. Additional sections include mitigation measures and suggestions for detecting the use of this technique in your environment.
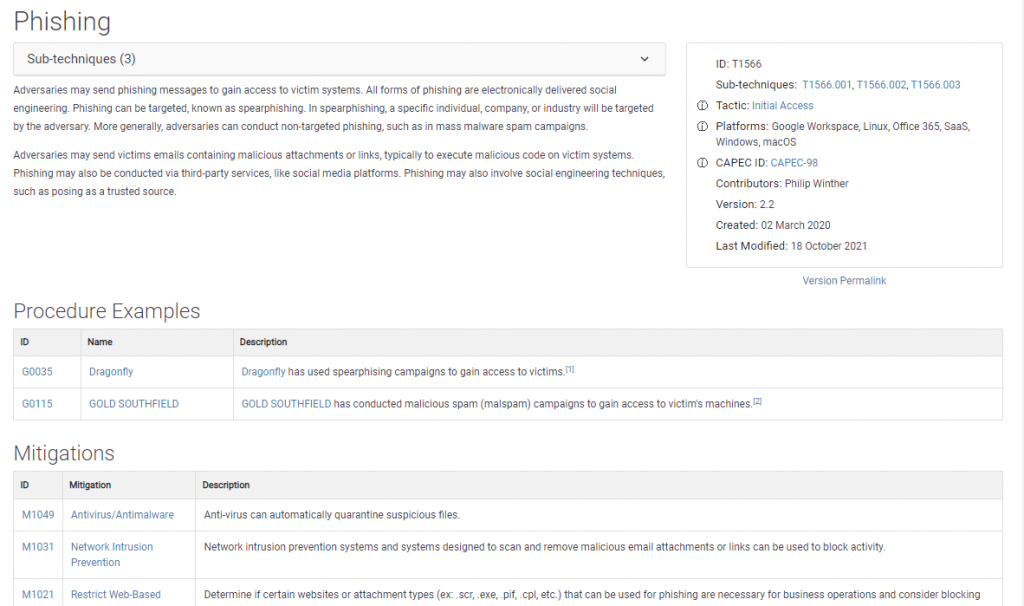
Figure 5
When you return to the full matrix, clicking the gray bar to the right of any technique reveals its sub-techniques. Figure 6 shows Sub Techniques of Phishing under the Initial Access tactic.
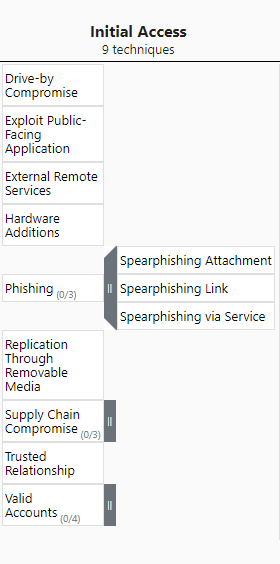
figure 6
Click on a sub-technique’s name to view detailed information. The figure 8 below shows the detail page for Phishing: Spear phishing Link. While both have similar descriptions and metadata. This detail page has far more procedure examples than the Phishing page (see Figure 5). In fact, there are 45. In actual attacks, The procedures describe the various ways a technique or sub-techniques used. It is possible to gain insight into both routine and sometimes novel ways adversaries. By using techniques, tools, and malware to accomplish their goals by studying the abundance of examples. The sheer number of documented instances is also an indication of how successful (popular) this sub-technique is with attackers.
This is a good opportunity to emphasize that some tactics and sub-tactics can be listed in more than one place. Spear phishing Link, for example, also appears under the Reconnaissance tactic (see Figure 8) as a sub-tactic of Phishing for Information. This description is nearly identical to that of the Initial Access: Phishing tactic shown in Figure 7. In Figure 8, however, the metadata lists a different ID number, “Sub-technique of” number, and tactic. This technique performed as part of the pre-attack phase, as indicated by the platform PRE. There are fewer entries here than in the preceding list because these procedures were performed as part of Reconnaissance rather than as part of an attempt to gain Initial Access.
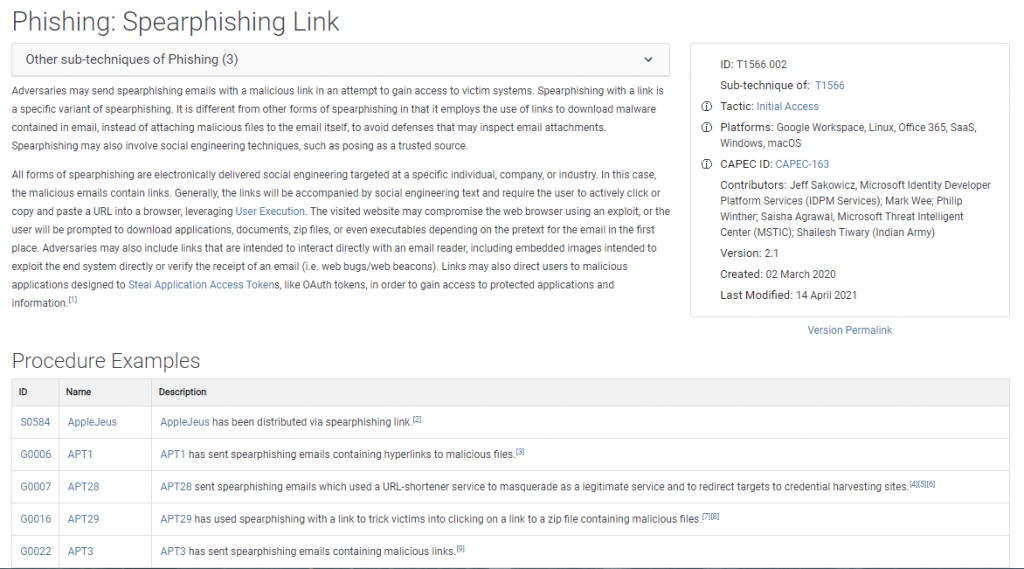
Figure 7
ATT&CK meticulously documents all data so you can review and compare the original sources of information to your organization’s own data, research, insights, history of adversary activity, etc.

Figure 8
Most people who are unfamiliar with MITRE ATT&CK focus so closely on the matrices that they are not aware of three additional invaluable resources: MITRE’s knowledge base of APT groups, its list of software used by adversaries, and the ATT&CK Navigator. Let’s start with Groups.
The ATT&CK database is one of the best and most comprehensive sources for public information on threat groups. The Groups section in the navigation bar provides information about known and suspected groups, along with their histories, habits, and observed malicious behaviors. Typically, the word group refers to known or suspected APT groups. In some cases, it refers to a group of interconnected intrusive activities or tools that can’t be assigned to a specific group. Blue Mockingbird is a good example of this: ATT&CK describes it as both a cluster of observed activity involving Monero cryptocurrency-mining payloads and a set of tools.
Figure 9 shows that each group has an ID number and a name, which can be clicked to display details. ATT&CK version 9 provides information on 122 groups (you can scroll through them quickly in the left pane). Since organizations often refer to groups by different names (and attribute different activities to different groups). The Group detail pages also list other associated group names and descriptions.
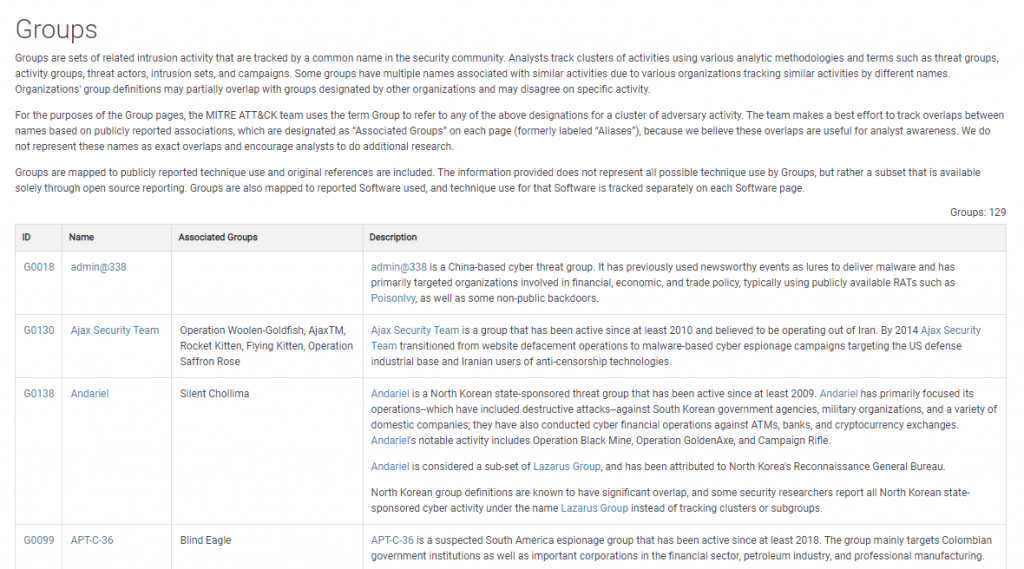
Figure 9
APTs are known to use 585 entries of software listed on the Software page in ATT&CK. The term software is used broadly and refers primarily to malicious software. However, it also includes commercially available, custom, and open-source code, as well as tools and some operating system utilities (such as ifconfig in UNIX or netsh in Windows) that aid in attacks (see Figure 10).

Figure 10
Click any of the IDs or names to see detailed descriptions of how, by whom, and for what purpose the software has been used. This figure shows a portion of the detail page for the malware loader Emotet. The complete list includes 24 techniques, many of which have further sub-techniques. Associated Software Descriptions also list other names by which software is known.
ATT&CK Navigator eliminates the headache of using spreadsheets or other tools to analyze threats, evaluate defenses, plan attacks, compare different elements that ATT&CK tracks, and more. Figure 11, illustrates the various techniques used by Dridex and ZeusPanda banking trojans. The tab selected compares the two. Dridex techniques are displayed in yellow, ZeusPanda techniques in red, and techniques shared by both are displayed in green. ATT&CK Navigator1 is just one example of the many ways it can be used for analysis, planning, attack simulations, and more.

Figure 11
Image Source: F5.com
ATT&CK provides businesses to enjoy several unique, core benefits. In the first place, the framework offers a deeper level of granularity and depth than traditional penetration testing. Various penetration testing exercises allow Red Teams to cover a wide range of techniques, tactics, and vectors.
ATT&CK also assists organizations in developing a common language and understanding of cyber threats within their organizations. When teams discuss things like Exfiltration or Lateral Movement. Mitigation and prevention can be better coordinated when members know which tactics fall under each umbrella.
Last but not least, ATT&CK Boost the overall cyber defense and incident response plans.. It is important for businesses to know which specific tactics they are most susceptible to so they can put in place the right safeguards. Your plan can be developed around that particular vector, for example, if the penetration testing using ATT&CK reveals that social engineering is most prevalent.
MITRE ATT&CK is a comprehensive and cross-referenced repository of information about real-world adversaries, their tactics, techniques, and procedures. Specific examples of their activities and the software and tools they employ to carry out their attacks (both legitimate and malicious). MTRE ATT&CK is a unique threat modeling and cyberattack lifecycle model designed from the attacker’s perspective and stands out from other defender-focused and risk-based models.
As a result, it is a unique tool for allowing organizations to gain insight into attacker behavior and improve their defenses accordingly. Contact an expert at Infosec Mates if you would like to learn more about how ATT&CK can improve your cybersecurity policy, penetration testing or incident response plan.